Summary
In June 2018, an Amnesty International staff member received a malicious WhatsApp message with Saudi Arabia-related bait content and carrying links Amnesty International believes are used to distribute and deploy sophisticated mobile spyware. Through the course of our subsequent investigation we discovered that a Saudi activist based abroad had also received similar malicious messages. In its analysis of these messages, Amnesty International found connections with a network of over 600 domain names. Not only are these domain names suspicious, but they also overlap with infrastructure that had previously been identified as part of Pegasus, a sophisticated commercial exploitation and spyware platform sold by the Israel surveillance vendor, NSO Group.
Malicious Messages sent to Activists working on Human Rights in Saudi Arabia
In early June, an Amnesty International staff member received a suspicious message on their personal mobile device. The message, delivered through the WhatsApp messenger, carried a malicious link which Amnesty International believes belongs to infrastructure connected with NSO Group and previously documented attacks (see below for more information on these connections).
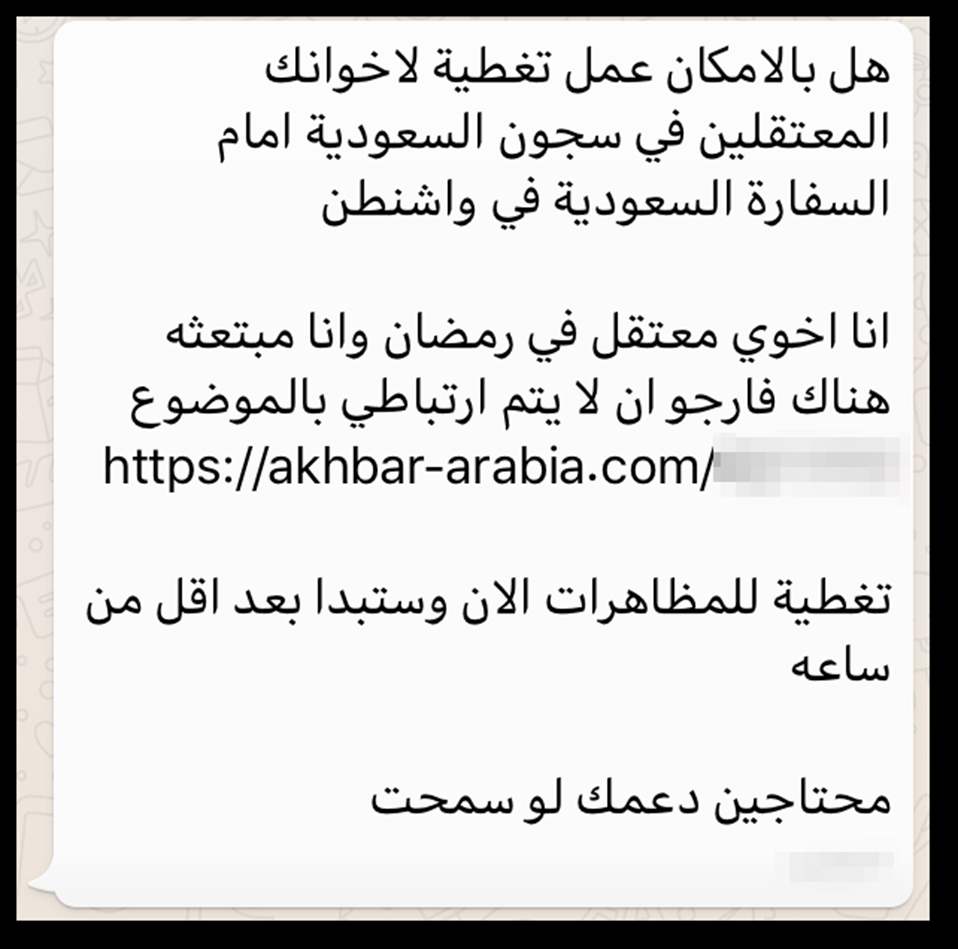

This WhatsApp message translates to:
“Can you please cover [the protest] for your brothers detained in Saudi Arabia
in front of the Saudi embassy in Washington.
My brother is detained in Ramadan and I am on a scholarship here so please do
not link me to this
[link]
Cover the protest now it will start in less than an hour
We need your support please”
While we did not include it in this publication, for security reasons, the sender’s number appears to belong to a commercial provider which among other services offers a virtual phone numbers management system, that allows customers to automatically send bulk SMS messages. This type of feature is normally used for promotional campaigns or other forms of automated systems. We believe the attackers might similarly be using this service to automate the process of sending malicious SMS and WhatsApp messages to deliver malware.
The message was clearly an attempt to trick our colleague into clicking on the link, which pointed to a domain name akhbar-arabia[.]com. As we will describe later in this report, we discovered this domain to belong to a large network infrastructure that has been previously documented to be connected to the Israeli surveillance vendor, NSO Group.
Through our investigation we identified one other human rights defender from Saudi Arabia, who also received malicious SMS messages. These messages carried links to domains which we identified as part of that same network infrastructure used by NSO Group or its customers to deliver exploits and malware designed to silently harvest data from the victims’ phones. This malware would allow an attacker complete access to the target’s phone or computer, essentially turning the device into a sophisticated eavesdropping and tracking tool to be used against them.
In late May, the activist received a message from an unknown number:

This SMS message translates to:
“Court order #XXXXXX issued against identity owner **** on XX/XX/XXX”
[link]”
As visible from the screenshot, the message included a link to the URL shortener service TinyURL. Through its website, we verified where this link redirected to a page located at the domain social-life[.]info
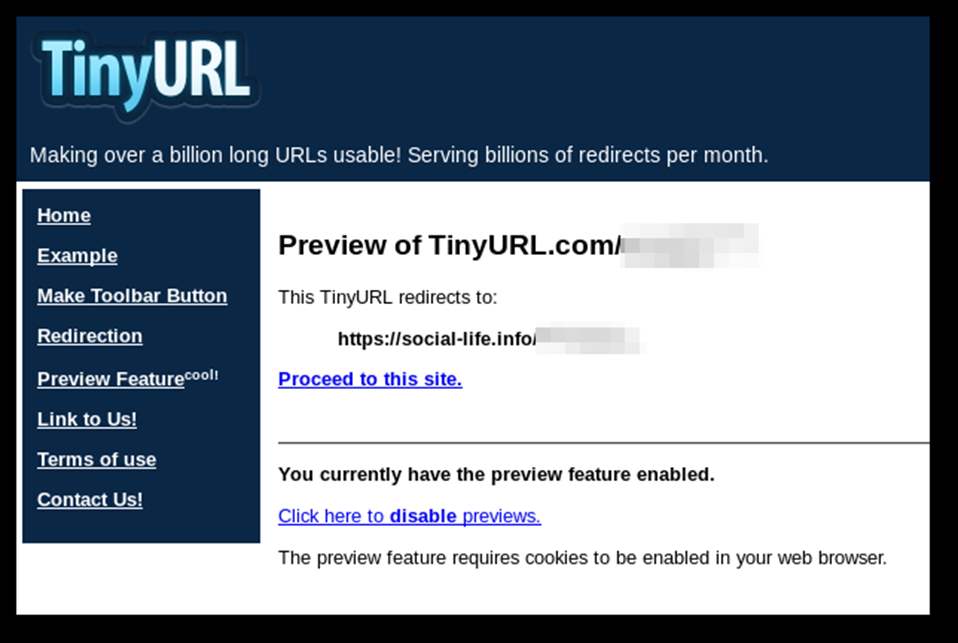
We also identified this domain to be connected to that same NSO Group’s infrastructure. In a report coordinated with this publication, Citizen Lab notes that the same domain has in fact been sent through very similar SMS messages to other people in the Gulf region.

The above screen shot is of a tweet sent out saying:
“You might receive a message on your phone telling you that you have a lawsuit filed under a specific number do not open the link in the message to avoid hacking your device there are various ways to hack mobile device be cautious.”
Shortly after, the activist received yet another suspicious message from an unknown number mentioning specifically the driving ban on women in Saudi Arabia. This was timely as just a few days earlier, women had been allowed to drive in Saudi Arabia following the state’s decision to lift a decades-old ban.
Interestingly, the text of the message is verbatim the title of Amnesty International’s press release, issued ahead of the decision to lift the ban entering into force.
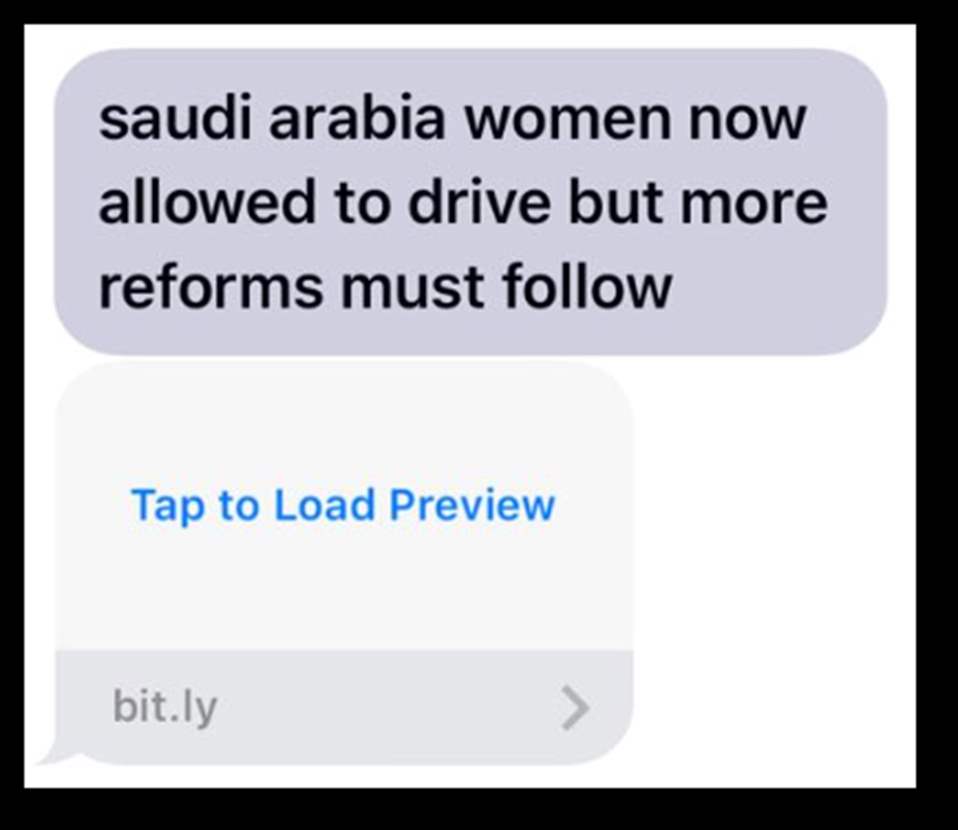
Unfortunately, because the bit.ly link had been disabled or deleted before we obtained copies of the message, we have not been able to confirm whether this was also carrying a link connected to known NSO Group’s infrastructure. However, it fits the same pattern as the earlier attack and is clearly trying to masquerade as information released by Amnesty International, presumably in an effort to trick the activist into clicking on the link.
Amnesty International contacted NSO Group with its findings, and they provided the following statement:
NSO Group develops cyber technology to allows government agencies to identify and disrupt terrorist and criminal plots. Our product is intended to be used exclusively for the investigation and prevention of crime and terrorism. Any use of our technology that is counter to that purpose is a violation of our policies, legal contracts, and the values that we stand for as a company. If an allegation arises concerning a violation of our contract or inappropriate use of our technology, as Amnesty has offered, we investigate the issue and take appropriate action based on those findings. We welcome any specific information that can assist us in further investigating of the matter.
Statement received by NSO Group on 31 July 2018
Why is this Wrong?
While law enforcement institutions in many countries have used secret surveillance in relation to national security objectives, Amnesty International as well as numerous other human rights organizations have documented cases where surveillance has been and continues to be carried out in a manner contrary to international human rights law – an important example being when people are targeted for surveillance based only on the exercise of their human rights. In these cases, surveillance would amount to an “arbitrary or unlawful” attack on their privacy or otherwise violate other human rights. Surveillance through the use of state-hacking tools such as those that NSO group provides is an extraordinarily invasive form of surveillance, and thus an especially problematic one under international human rights law and standards.
As laid out in the UN Guiding Principles on Business and Human Rights (UNGPs), companies have a responsibility to respect human rights wherever they operate in the world. The UNGPs require that companies take pro-active steps to ensure that they do not cause or contribute to human rights abuses within their global operations, and to respond to any human rights abuses when they do occur. In order to meet that responsibility, companies must carry out human rights due diligence to “identify, prevent, mitigate and account for how they address their human rights impacts.” The corporate responsibility to respect human rights exists independently of a state’s ability or willingness to fulfil its own human rights obligations and over and above compliance with national laws and regulations protecting human rights.
Defending human rights is not a crime. According to the Declaration on the Right and Responsibility of Individuals, Groups and Organs of Society to Promote and Protect Universally Recognized Human Rights and Fundamental Freedoms (commonly known as the Human Rights Defenders Declaration), Article 1:
Everyone has the right, individually and in association with others, to promote and to strive for the protection and realization of human rights and fundamental freedoms at the national and international levels.
Article 1, Declaration on the Right and Responsibility of Individuals, Groups and Organs of Society to Promote and Protect Universally Recognized Human Rights and Fundamental Freedoms
Amnesty International does just this – we strive for the protection and realization of human rights. Targeting Amnesty International and other human rights defenders for surveillance on the basis of our work can in no way be categorized as a legitimate use of NSO digital exploits.
How does NSO Group infrastructure work?
The functionality of Pegasus, the attack and surveillance platform sold by NSO Group, is accurately described in a document named “Pegasus – Product Description” that was found in the 2015 leak of the competing Italian spyware vendor, Hacking Team.
We can see from this document that the messages received by Amnesty International and others are described by NSO Group as “Enhanced Social Engineering Message” (ESEM).
When clicking on the link, the victim will be connected through a network of anonymizing nodes provided by NSO Group, which are designed to anonymize the final location of the Pegasus servers in a way that conceals the customer’s identity or origin.

A section of this documents describes these nodes as the Pegasus Anonymizing Transmission Network (PATN).
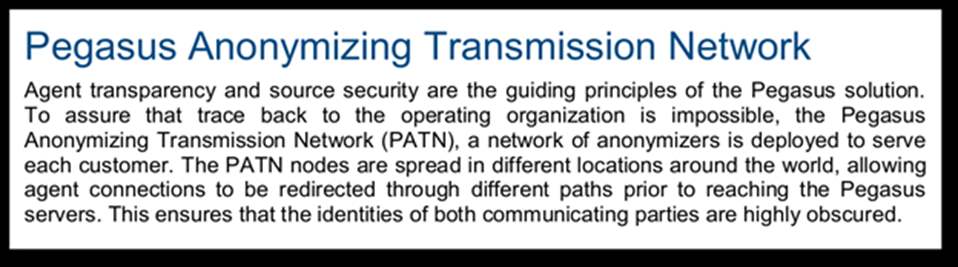
Ultimately, the victim would be taken to what is described as a Pegasus Installation Server which will attempt the exploitation of a vulnerable device and the silent installation of the Pegasus spyware.
As we tried to activate the infection by opening the link from a contained environment, we were instead redirected to a legitimate Saudi Arabian news site, The New Khalij, which indicates a failed attempt at activating any malicious behavior. This is consistent with the behavior described in the leaked Pegasus product description:
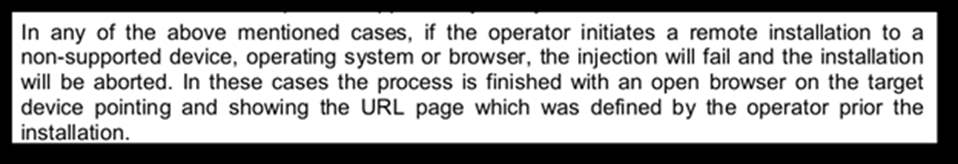
In order to avoid being discovered by security researchers and anti-virus vendors, advanced spyware producers often employ some form of verification of the device connecting to an exploitation server, and only deliver the spyware under very specific circumstances. For example, the attackers might configure the servers to only deliver the exploits to devices connecting from a particular country or devices running specific versions of Android or iOS. Most likely, we believe that NSO Group or its customers might configure the malicious links that are distributed to targets to be automatically deactivated after a very limited timeframe, for example 24 hours.
How do we know it’s connected to NSO Group?
In addition to the behavior of the servers we identified matching NSO Group’s description of Pegasus in the Hacking Team leaked document, we have found two other connections to NSO Group. One is evidence that connects the malicious links we received and collected with NSO Group network infrastructure that was previously discovered and publicly reported on by Citizen Lab. And, though more speculative, the second is a domain registration pattern showing that most of the domains in the NSO Group infrastructure were registered during Israeli working days and hours (where NSO is based).
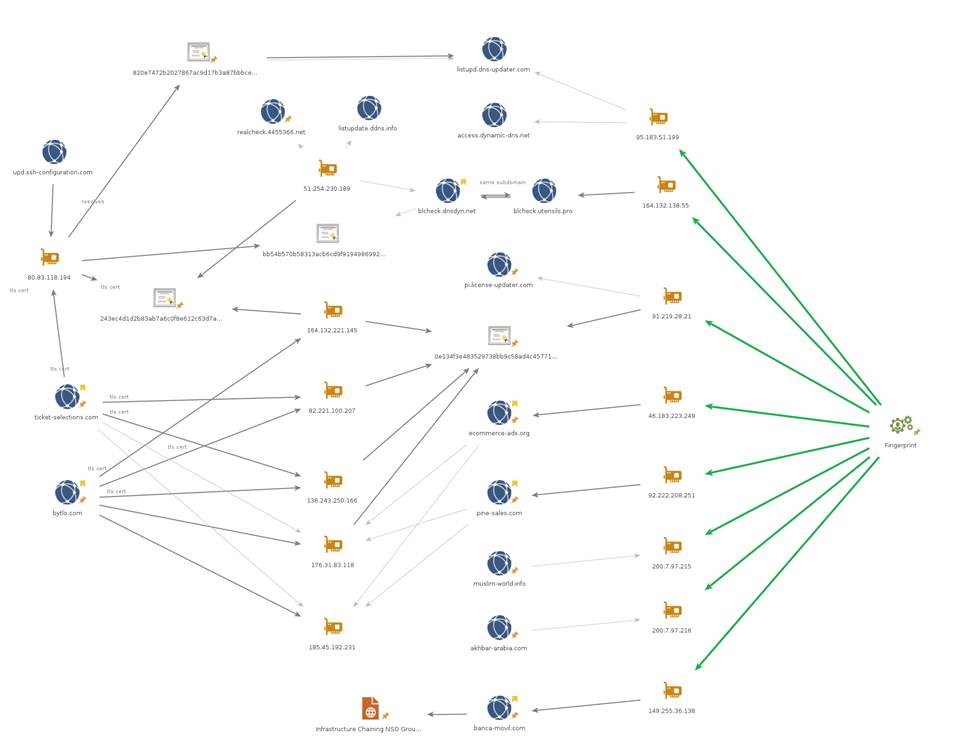
When analyzing the domains sent through SMS and WhatsApp messages to Amnesty International and others, we devised a technical methodology that allowed us to confidently identify whether a given server appears to be a PATN server. Because the links sent to targets are not legitimate webpages, but anonymizing nodes routing to an exploitation server, they demonstrate rather unique behavior that we can synthesize to form a “fingerprint”.
This fingerprint is a combination of different technical elements, including a particular cryptographic configuration used by the servers to offer encrypted transports, the exposure of certain services rather than others, and certain circumstances that cause the server to abruptly interrupt connections. Using this fingerprint, we are then able to perform a probe of internet-facing servers and identify those that demonstrate behavior which is similar to that of the servers we have seen in the malicious messages, namely akhbar-arabia[.]com and social-life[.]info. The Censys.io project generously provided us with access to their datasets which allowed us to optimize our internet scans.
With the technique we developed, we were then able to identify over 600 servers that demonstrated similar behavior. Among these we found servers that hosted domain names that have been previously identified as connected to NSO Group by Citizen Lab and others, specifically banca-movil[.]com, pine-sales[.]com, and ecommerce-ads[.]org.
| IP Addresses found in our scanning | Domain names connected the IP |
| 149.255.36.138 | banca-movil[.]com |
| 92.222.208.251 | pine-sales[.]com |
| 46.183.223.249 | ecommerce-ads[.]org |
We have also identified a set of self-signed TLS certificates, cryptographic documents that secure and identify a given website, which were shared between the infrastructure identified by Citizen Lab in 2016 and the new infrastructure we have identified with our scanning techniques.
The server pi.license-updater[.]com (91.219.28.21) matched our server fingerprint. Previously this IP served the self-signed certificate with fingerprint 0e134f3e483529738bb9c58ad4c45771681796d7. Using public network data repositories, such as RiskIQ Passivetotal, we can see that this certificate was also served on IP addresses 176.31.83.118, 82.221.100.207, 136.243.250.166, and 164.132.221.145.
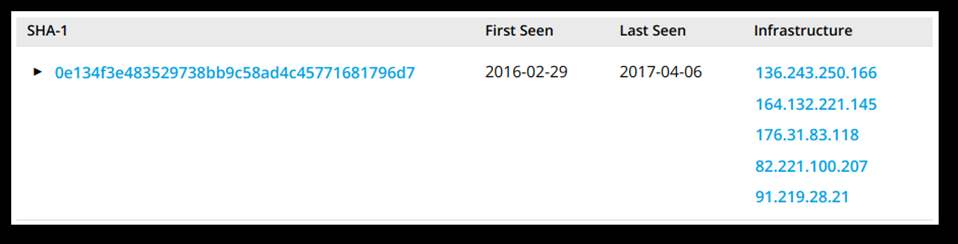

As shown in the following table, the domains bytlo[.]com, ticket-selections[.]com, pine-sales[.]com and ecommerce-ads[.]org have all previously resolved to 176.31.83.118. All four of these domains were identified by Citizen Lab. The domains pine-sales[.]com and ecommerce-ads[.]org are still online but now point to new servers. Both of these new servers match our fingerprint.
| Domain discovered by Citizen Lab in 2016 | IP Address the domains resolved to in 2016 |
| bytlo.comticket-selections.compine-sales.comecommerce-ads.org | 176.31.83.118 |
| bytlo.comticket-selections.compine-sales.comecommerce-ads.org | 185.45.192.231 |
The server at 164.132.221.145 has previously served another self-signed TLS certificate with fingerprint 243ec4d1d2b83ab7a6c0f8e612c63d7ab62f028a. RiskIQ shows that this certificate was also served on 80.83.118.194, 51.254.230.189, and 164.132.221.145.
The IP address 80.83.118.194 has previously served certs for blcheck.dnsdyn[.]net, listupd.dns-updater[.]com, and ticket-selections[.]com. The hostname listupd.dns-updater.com previously resolved to the IP address 95.183.51.199. This IP address is now serving a TLS certificate for access.dynamic-dns[.]net. This server matches our fingerprint.
The IP address 51.254.230.189 has also previously served a valid certificate for blcheck.dnsdyn[.]net. This subdomain part of the hostname matches another hostname, blcheck.utensils[.]pro (164.132.138.55) which we have identified as part of our scanning. We assume that these domains are a set of internal servers used for testing or maintaining the PATN network.
This is more clearly visualized in the graph below:

As previously mentioned, Citizen Lab has also been conducting similar scanning efforts over the last couple of years and have independently come to the same conclusions. In their report, also published today, they disclose some of their discoveries that corroborate our findings and provide further evidence.
While speculative, we have also performed an analysis of the registration dates and times of the hundreds of PATN domains we identified. This analysis is based on publicly available data that domain registrars collect from their customers when selling any new domain name. This information (which can be accessed through any so-called WHOIS lookup service) can look something like the following:
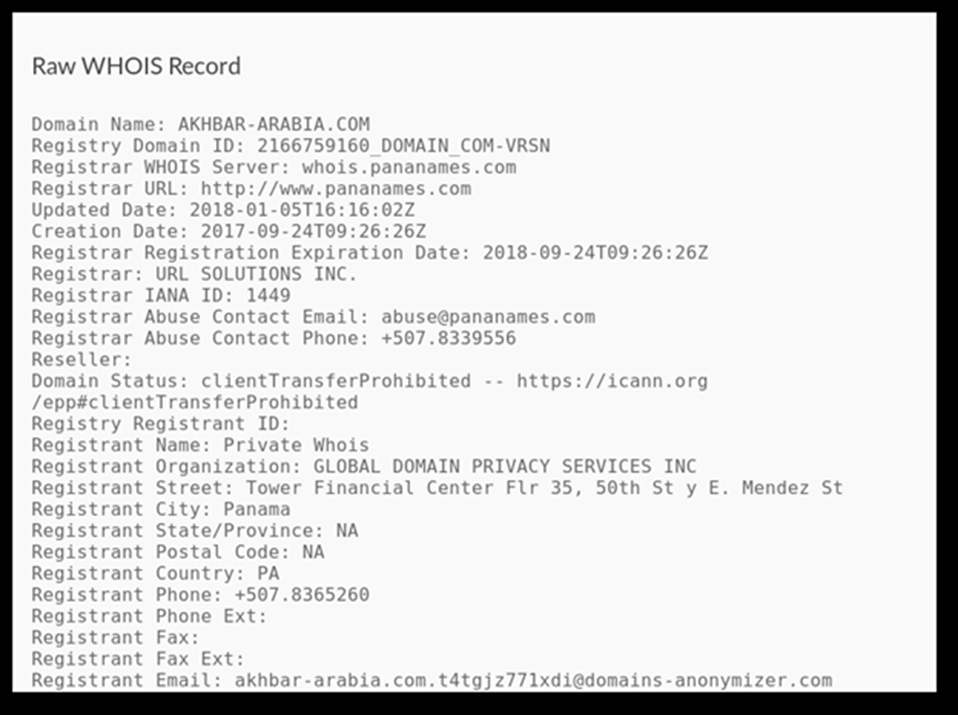

The information about the “Registrant” would normally provide information about the customer that acquired the domain name, bearing in mind that this information is often fake, especially when the domain is used for malicious purposes. However, given that the registration date is normally public and reliable, we chose to collect the registration date of all the domains we discovered and looked for patterns.
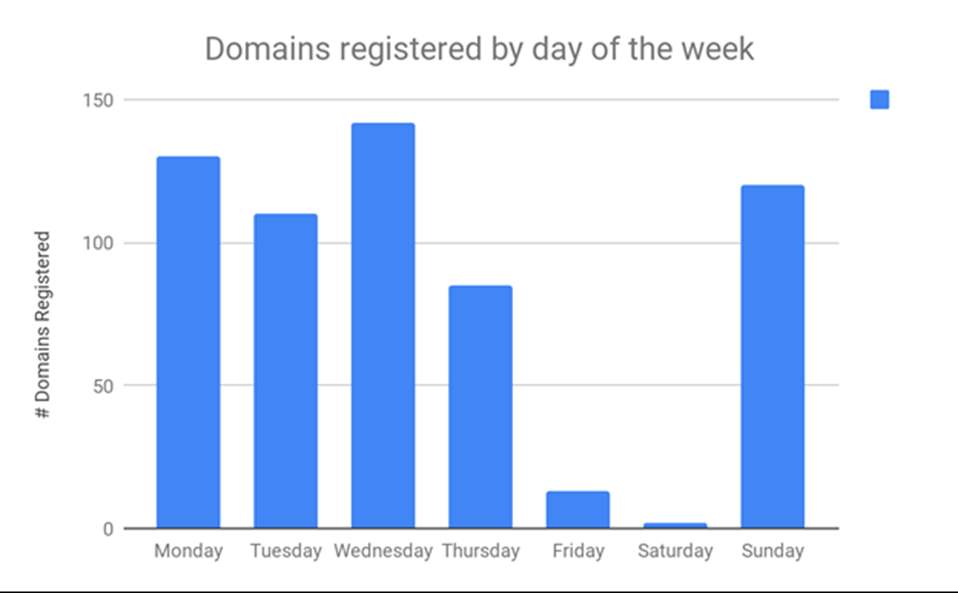
The following graph shows that the vast majority of domain names were registered between Sundays and Thursdays, which matches the Israeli work week (recognising of course that this is the working week of several other countries as well).

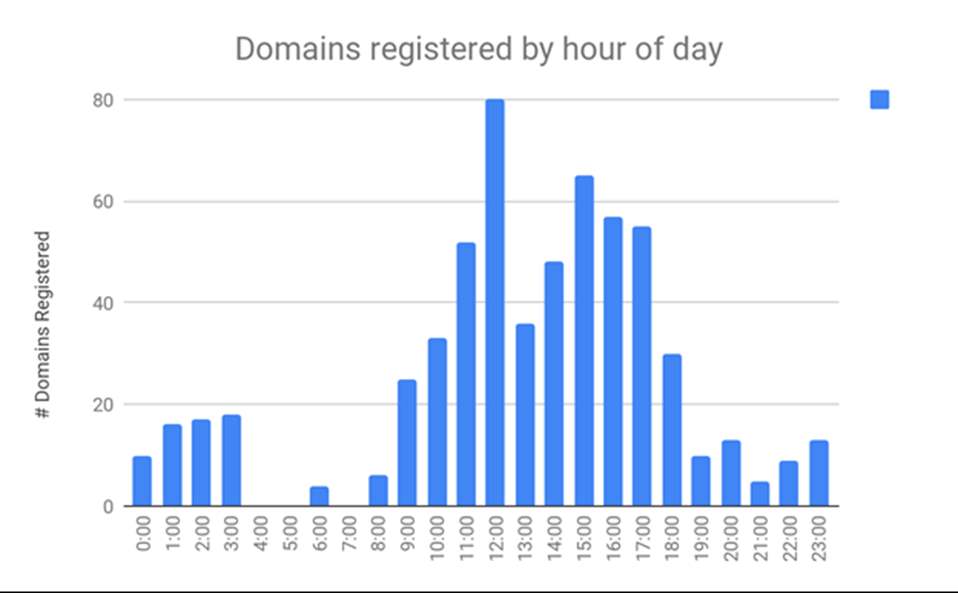
We did the same analysis for hours of the day when most domain names were registered. The following graph shows the distribution of domains by hour in Tel Aviv’s time zone. Interestingly, the highest concentration is between 9am and 6pm, which matches regular working hours in Israel, where NSO Group is based.
Hundreds of domains reveal potential use
As mentioned, through the fingerprint scanning efforts we described, we identified approximately 600 hosts which are clustered among a limited set of registrars, name servers and hosting providers.
NOTE: Because we cannot know how specifically each and every one of the domains we discovered has been or is being used by any of NSO Group’s customers, we are not disclosing the full list at this time. We will wait a grace period of two months after which we will provide the full list of domains to the public research and security community. The domains mentioned specifically in this publication are ones we consider relevant as possible threats to civil society and human rights defenders.
Domains suggesting presence in certain countries
Out of the hundreds of domains we identified through our internet scanning, certain patterns indicate deployments relevant certain countries.
For example, a number of domains using country code such as “zm” would suggest a deployment relevant to Zambia, highlighted by the use of “zm” as a suffix or prefix.
| onlineshopzm[.]com |
| zednewszm[.]com |
| zm-banks[.]com |
| zm-weather[.]com |
Other domains refer to specific geographical regions, such as maybe Congo:
| nothernkivu[.]com | References to North Kivu, a region in the Democratic Republic of the Congo |
Or more generally relevant to Africa:
| afriquenouvelle[.]com |
| allafricaninfo[.]com |
We also found numerous domains that suggest deployments relevant to Russian-speaking countries, for example:
| centrasia-news[.]com | Spoofing Central Asia News (https://ca-news.org/), popular among opposition activists |
| mystulchik[.]com | Stulchik is Russian for a small chair, perhaps a combination of English and Russian? |
| odnoklass-profile[.]com | Spoofing “Odnoklassniki” a social media network popular in Russian speaking countries |
| sputnik-news[.]info | Sputnik News (https://sputniknews.com) |
Numerous domains suggest more conclusively a deployment relevant to Kazakhstan:
| tengrinews[.]co | Spoofing the legitimate news website Tengri News (tengrinews.kz) |
| sergek[.]info | sergek.kz is a video surveillance system in Kazakhstan |
| egov-sergek[.]info | Egov.kz is an electronic government site in Kazakhstan |
| egov-segek[.]info | This seems similar to the link above |
| mykaspi[.]com | Spoofing Kaspi, a banking institution from Kazakhstan |
| kaspi-payment[.]com | Spoofing Kaspi, a banking institution from Kazakhstan |
Some other domains might suggest targets from Latvia, because of the use of Latvian words:
| e-sveiciens[.]com | “e-greetings” in Latvian |
| klientuserviss[.]com | “Client service” in Latvian |
| kurjerserviss[.]com | “Customer service” in Latvian |
| reklamas[.]info | “Advertisement” in Latvian |
Another domain suggests use in Hungary:
| legyelvodas[.]com | Hungarian language link that may be designed to appear to relate to Vodafone |
Impersonating News Websites
We found several domains that seek to impersonate news websites:
| theastafrican[.]com | Impersonating the Kenyan newspaper The East African (https://www.theeastafrican.co.ke/) |
| ajelnews[.]net | Impersonating the Saudi Arabian news website Ajel News (https://ajel.sa) |
| akhbara-aalawsat[.]com | Possibly impersonating the Arabic news website Asharq Al-Awsat (https://aawsat.com) |
| centrasia-news[.]com | Spoofing Central Asia News (https://ca-news.org/), popular among opposition activists. |
| tengrinews[.]co | Impersonating the Kazakhi news website Tengri News (https://tengrinews.kz) |
| akhbar-arabia[.]com | Possibly impersonating the Arabic news website Akhbar Arabia (https://akhbararabia.net/) |
| gulf-news[.]info | Possibly impersonating Gulf News (https://gulfnews.com) |
| eltiempo-news[.]com | Impersonating the Colombian newspaper El Tiempo (https://eltiempo.com) |
| sputnik-news[.]info | Sputnik News (https://sputniknews.com) |
We also identified numerous domains that more generally pose as news websites:
| arabnews365[.]com |
| arabworldnews[.]info |
| breaking-extranews[.]online |
| breaking-news[.]co |
| breakingnewsasia[.]com |
| breakthenews[.]net |
| daily-sport[.]news |
| diaspora-news[.]com |
| discoveredworld-news[.]com |
| eurosportnews[.]info |
| golf-news[.]live |
| investigationews[.]com |
| islamic-news-today[.]com |
| kingdom-news[.]com |
| leadersnews[.]org |
| news-alert[.]org |
| news-gazette[.]info |
| newscurrent[.]info |
| newsdirect[.]online |
| newsofficial[.]info |
| newsofthemoment[.]net |
| newworld-news[.]com |
| online-dailynews[.]com |
| only-news[.]net |
| operatingnews[.]com |
| posta[.]news |
| regionews[.]net |
| topten-news[.]info |
| zednewszm[.]com |
Conclusions
NSO Group is one of the most secretive surveillance technology manufacturers in the world. Throughout 2016 and 2017, the Canadian research group Citizen Lab, from the University of Toronto, published numerous reports on the alleged use of a spyware for mobile called “Pegasus”, developed by the Israeli company NSO Group. The original discovery of this potent spyware was made possible thanks to Ahmed Mansoor, a prominent human rights defender from the United Arab Emirates (UAE), who shared the messages sent to his phone containing Pegasus with Citizen Lab. His actions sparked a long investigation that would later reveal similar attacks in Mexico against scientists, lawyers and activists.
| Ahmed Mansoor has been targeted with sophisticated spyware at least twice previously, including using tools created by the German-British Gamma Group and the Italian Hacking Team. Mansoor was arrested in March 2017 and held mostly in solitary confinement until he was eventually convicted and sentenced to 10 years in prison and fined 1,000,000 Emirati Dirham (approximately USD $270,000) in May 2018, for posts he made on social media in connection with his human rights work.The prosecution characterized his so-called crime as “publish[ing] false information to damage [the] UAE’s reputation abroad” and “portray[ing] the UAE as a lawless land.” He is a prisoner of conscience and Amnesty International is calling for his immediate and unconditional release. |
In this blog post, we have aimed to demonstrate that the WhatsApp message received by our colleague was more than just a text message. It was a digital attack on our staff member’s privacy rights and on our role as a human rights organization. While secret surveillance may have legitimate uses by states in some contexts – this attack against us is not one. Moreover, when viewed against the history of attacks against civil society in other countries like the UAE and Mexico, it paints a disturbing picture of the ways in which NSO Group technologies are being abused globally.
Even more disturbing is the fact that we identified over 600 domains that represent potential threats to human rights defenders and civil society actors in countless other countries around the world.
We all have the right to associate, communicate and share information about human rights threats, issues and violations related to ourselves or to others. The unchecked use of surveillance technologies such as those produced by NSO Group can have a serious silencing effect on civil society. Someone doesn’t even need to actually be spied on to feel the repressive reach of the surveillance industry – especially when our interest in human rights is knowingly and purposefully used as bait.
Defending human rights is not a crime.
Update
On 01 October 2018, after waiting a grace period of two months, we provided the full list of domains to the public research and security community. This list of domains can be found on Github and PassiveTotal.


